A Hardware Security Module (HSM) is a specialized device that provides a secure environment for safeguarding and managing cryptographic keys, as well as performing cryptographic operations. It is designed to protect the confidentiality, integrity, and availability of sensitive data by offering robust physical and logical security measures. In this article, we will delve into the intricacies of HSMs, exploring their features, use cases, benefits, and industry standards.
What is a Hardware Security Module (HSM)?
A Hardware Security Module is a tamper-resistant, secure hardware device that is built to protect and manage cryptographic keys and perform cryptographic operations such as encryption, decryption, signing, and verification. It is typically implemented as an external device, connected to a host system (such as a server or a network appliance) through a secure interface, such as a USB or PCIe.
Features of Hardware Security Modules
1. Physical Security: HSMs are designed to withstand physical attacks, ensuring the integrity of the device and the confidentiality of the stored cryptographic keys. They are often built with tamper-evident seals, sensors, and self-destruct mechanisms to prevent unauthorized access or tampering.
2. Key Management: HSMs provide a secure environment for generating, storing, and managing cryptographic keys. They offer key lifecycle management functionalities, including key generation, import/export, backup, rotation, and destruction. HSMs can also enforce policies for key usage, such as access control, separation of duties, and dual control.
3. Cryptographic Operations: HSMs support a wide range of cryptographic algorithms and operations, including symmetric key encryption, asymmetric key encryption, digital signatures, random number generation, and secure hashing. They offer high-performance hardware-accelerated cryptographic operations, ensuring efficient and secure data processing.
4. Secure APIs: HSMs provide software libraries and APIs (Application Programming Interfaces) that allow developers to integrate cryptographic functionalities into their applications. These APIs abstract the complexity of the underlying cryptographic operations and provide a standardized interface for interacting with the HSM.
Use Cases of Hardware Security Modules
1. Financial Institutions: HSMs are widely used in the financial industry to secure payment transactions, ATM networks, and online banking systems. They protect cryptographic keys used in PIN encryption, card issuance, secure messaging, and transaction verification, ensuring the integrity of financial transactions.
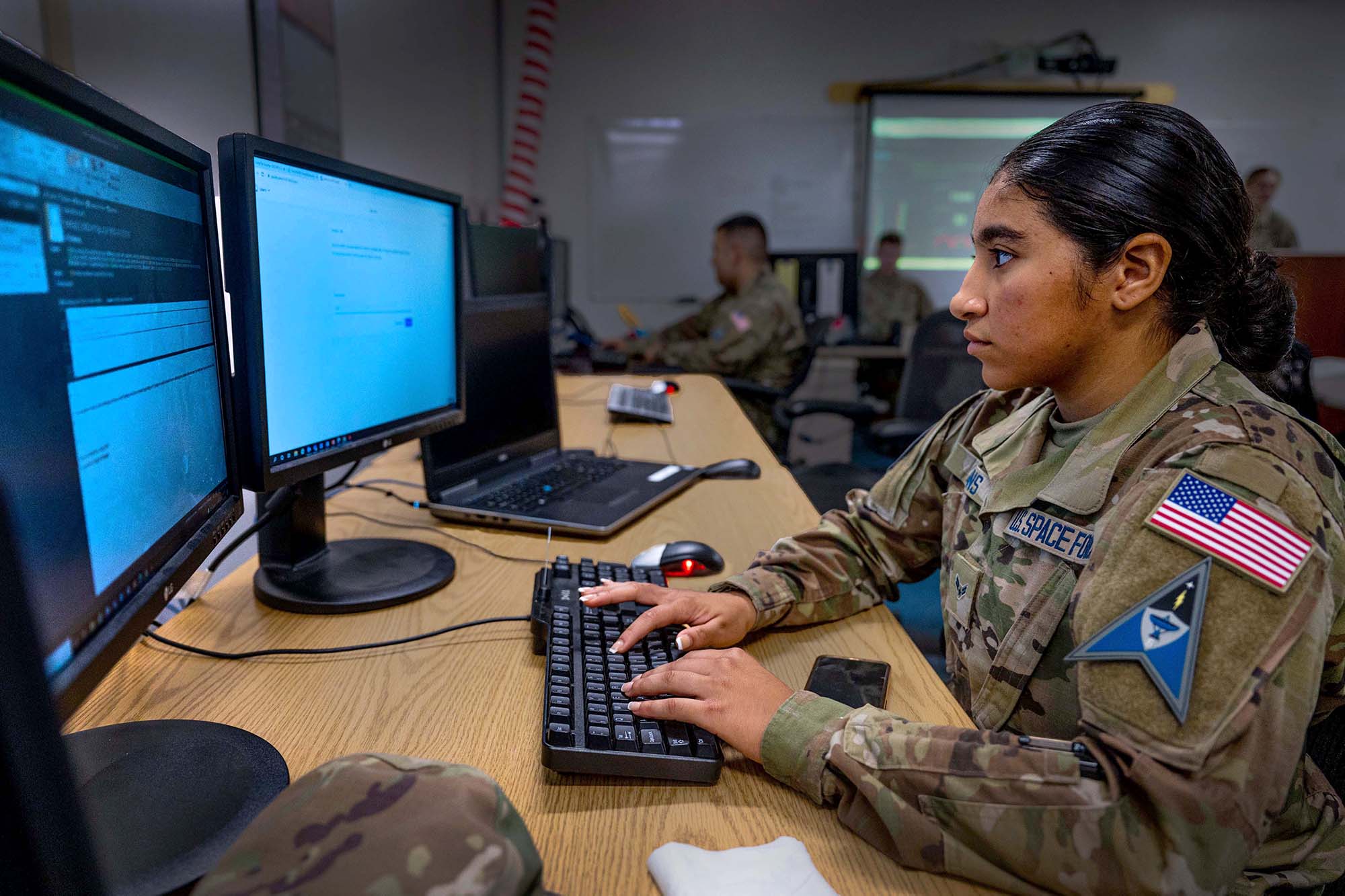
2. Government and Defense: HSMs play a crucial role in securing sensitive government and defense systems. They are used to protect classified information, secure communication channels, authenticate digital identities, and ensure the integrity of critical infrastructure.
3. Cloud Service Providers: HSMs are employed by cloud service providers to offer secure key management and cryptographic services to their customers. They enable customers to protect their data and applications in the cloud, ensuring that cryptographic keys are stored and processed securely within the HSM.
4. IoT and Connected Devices: With the proliferation of Internet of Things (IoT) devices, HSMs are increasingly used to secure the communication and data exchange between connected devices. They provide end-to-end encryption, secure bootstrapping, and device authentication, ensuring the privacy and integrity of IoT communications.
Benefits of Hardware Security Modules
1. Enhanced Security: HSMs offer a higher level of security …
Read More