Which L-formed gaming personal computer desk is most effective?
For a lot of gaming established-ups, actual estate is almost everything. That means that the much more area out there on the desk, the extra room there is for all the most effective peripherals like keyboards and gaming mats, guaranteeing the best gaming aesthetic.
L-formed gaming pc desks provide enough amounts of area when also obtaining the versatility of fitting into the corners of any area to generate the excellent gaming natural environment, building them a excellent notion when you’re on the hunt for your upcoming gaming desk.
Attributes of L-formed gaming computer desks
Multi-watch guidance and dimensions
Quite a few gaming established-ups now need extra than one keep track of to independent perform and participate in on diverse screens or even hold chat tabs open up on 1 though the activity performs on a different. Thanks to the enough area that L-formed desks offer, having more than one particular keep track of is simpler than ever. Also, sure gaming desks have precise mounts or sites particularly for screens. Other individuals only permit customers to area their displays wherever they like.
Price
The rates of gaming desks change tremendously. Owing to the limitless kinds of gaming set-ups out there, desks mirror those people various approaches by means of layout and functionality. The most low-cost gaming desks price tag about $80-$100, enabling for at the very least one gaming keep track of and space for your peripherals. More highly-priced gaming desks will generally charge $100-$200 and are usually much more spacious. Most L-formed gaming desks will fall into this class as they ordinarily provide considerably far more place than more cost-effective designs, this kind of as certain placement for your screens. Last but not least, the most high-priced gaming desks will frequently value far more than $200 and have far more capabilities included onto them, this kind of as height changes and drawer area.
Ergonomics
Ergonomics refers to learning people’s efficiency in their operating environments, and many present-day desks are now applying ergonomic types into their merchandise. Some ergonomic characteristics can involve extra leg area underneath the desk for stretching or an adjustable top feature to boost posture and do the job effectiveness. The outcome is much more snug models to help in sitting for very long durations, regardless of whether for gaming, working or streaming.
The greatest L-formed gaming laptop or computer desks
Ideal of the ideal L-formed gaming laptop desk
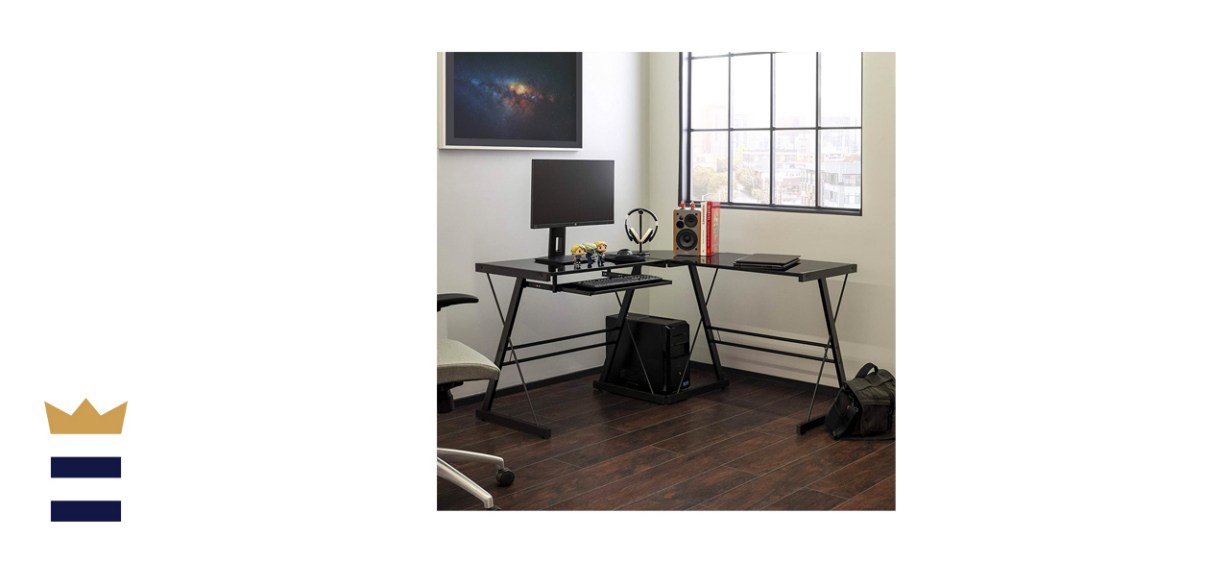
Walker Edison Ellis Contemporary Glass Leading L Formed Corner Gaming Desk
The Walker Edison gaming desk presents top customizability in different models, letting it be a straight desk, an L-formed desk and a U-shaped desk all in 1. Each individual area supports up to 50 lbs each individual, with the corner pieces can support up to 20 pounds and the keyboard tray supporting up to 10 lbs.
It is uncomplicated to assemble and reassemble, generating it handy to conform to any sort of gaming setup. The 1 downside is that