Table of Contents
Scientists at the University of Cyber Stability at Korea College, Seoul, have presented a new covert channel attack named CASPER can leak data from air-gapped pcs to a nearby smartphone at a rate of 20bits/sec.
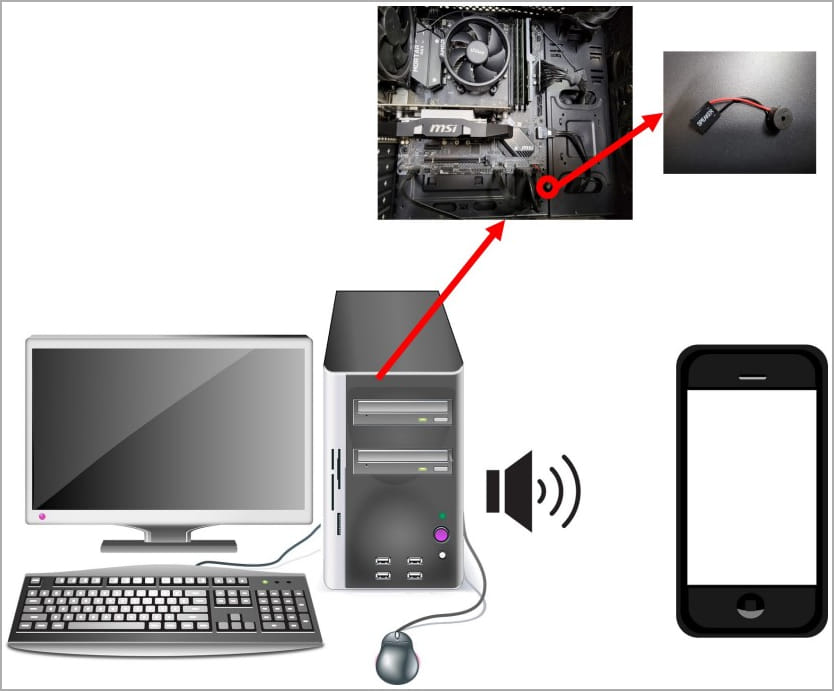
The CASPER attack leverages the interior speakers inside the target laptop or computer as the information transmission channel to transmit large-frequency audio that the human ear can not hear and convey binary or Morse code to a microphone up to 1.5m away.
The obtaining microphone can be in a smartphone recording sound inside the attacker’s pocket or a notebook in the same room.
Researchers have formerly designed very similar assaults leveraging exterior speakers. Nonetheless, air-gapped, network-isolated techniques employed in essential environments, this sort of as authorities networks, energy infrastructure, and weapon regulate methods, are unlikely to have external speakers.
On the other hand, interior speakers that offer audio feed-back, this kind of as boot-up beeps, are continue to viewed as required, so they are typically present, earning them far better candidates.
Infecting the concentrate on
As is the case with pretty much all magic formula channel attacks concentrating on community-isolated desktops, a rogue employee or a stealthy intruder with physical entry to the concentrate on will have to first infect it with malware.
Though this scenario may well feel impractical or even considerably-fetched, there have been a number of situations of such attacks getting productively carried out in the previous, with notable examples together with the Stuxnet worm, which qualified Iran’s uranium enrichment facility at Natanz, the Agent.BTZ malware that infected a U.S. armed forces foundation, and the Remsec modular backdoor, which secretly gathered information and facts from air-gapped federal government networks for above five several years.
The malware can autonomously enumerate the target’s filesystem, locate data files or file types that match a hardcoded list and try to exfiltrate them.
Extra realistically, it can conduct keylogging, which is far more appropriate for these types of a sluggish details transmission rate.
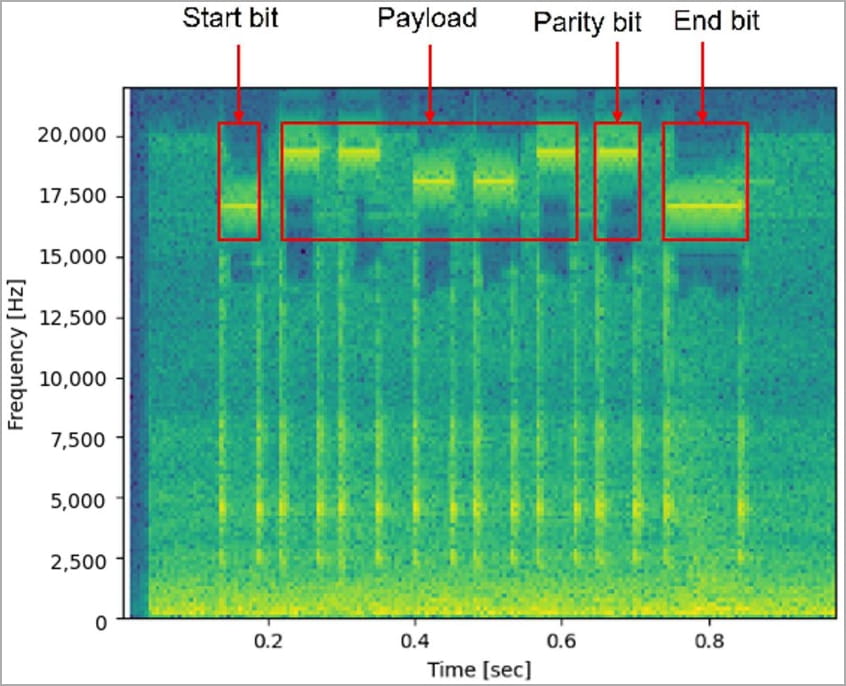
The malware will encode the info to be exfiltrated from the goal in binary or Morse code and transmit it through the inner speaker utilizing frequency modulation, acquiring an imperceptible ultrasound in a selection amongst 17 kHz and 20 kHz.
The benefits
The scientists experimented with the explained model making use of a Linux-based mostly (Ubuntu 20.04) computer system as the concentrate on, and a Samsung Galaxy Z Flip 3 as the receiver, running a essential recorder application with a sampling frequency of up to 20 kHz.
In the Morse code experiment, the scientists established the duration for each little bit to 100 ms and made use of 18 kHz for dots and 19 kHz for the dash. The smartphone was found 50cm away and was capable to decode the sent term “covert.”
In the binary data experiment, the size per little bit was set to 50 ms, transferring zeros at a frequency of 18 kHz and 1s at 19 kHz. A 50 ms commence/conclude bit was also used at 17 kHz to reveal the starting of a new concept.
Dependent on the done tests, the optimum length of the receiver is 1.5 meters (4.9 ft), making use of a size per little bit of 100 ms.
The overall benefits of the experiment, nonetheless, demonstrate that the length per little bit has an effect on the little bit mistake fee, and a most trusted transmitting little bit charge of 20 bits/s is achievable when the duration for each bit is 50 ms.
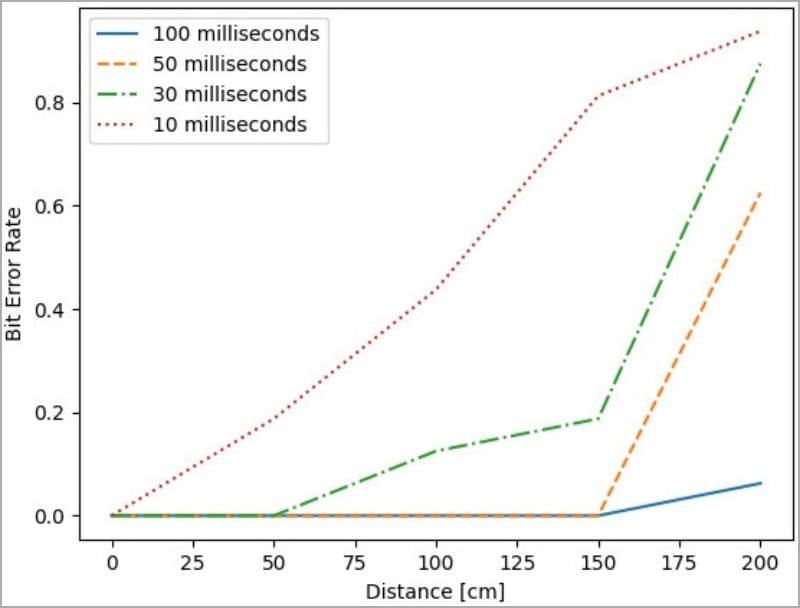
At this information transfer level, the malware could transmit a typical 8-character size password in about 3 seconds and a 2048-bit RSA crucial in 100 seconds.
Anything at all earlier mentioned that, like a tiny 10 KB file, for illustration, would require around an hour to exfiltrate from the air-gapped system, even if the circumstances are excellent and no interruptions happen for the duration of the transmission.
A solution to the slow information amount would be to change the frequency band for a number of simultaneous transmissions on the other hand, internal speakers can only produce audio in a solitary frequency band, so the attack is nearly limited.
The scientists shared methods to protect against the CASPER attack, with the easiest getting to remove the interior speaker from mission-crucial pcs.
If that is not possible, defenders could put into practice a higher-go filter to hold all created frequencies within the audible seem spectrum, blocking ultrasound transmissions.
If you might be fascinated in other covert channel assaults against air-gapped techniques, examine out COVID-bit, which makes use of the PSU to produce electromagnetic waves that carry knowledge.
Other illustrations of similar assaults are ETHERLED, which relies on the LED lights of the target’s network card to transmit Morse code alerts, and a single named SATAn, which makes use of SATA cables as wi-fi antennas.





