Immediately after a relatives intervention involving his father, the present-day U.S. president, Hunter Biden was despatched to a rehab facility in Maryland. But, he hardly ever checked in.
In element 4 of the Fox Country unique “Who is Hunter Biden?,” Decide Jeanine Pirro tracks Hunter’s “drugged, befuddled blur of total and utter debauchery” to a pc maintenance store that arrived into the possession of Hunter’s infamous laptop computer.
“I could surely inform that he was inebriated,” mentioned John Paul Mac Isaac, the previous operator of “The Mac Store” in Wilmington, Delaware. Mac Isaac instructed Fox Nation that Hunter entered his shop on April 12, 2019, just right before closing time.
HUNTER BIDEN’S ‘DEBAUCHERY’: Choose JEANINE Taps INTO A Lifestyle OF Intercourse, Medicine AND Overseas FUNDING
“When I asked for his final identify, there was a lengthy pause. And he kind of sarcastically additional Biden. I had to ask Hunter for his password. And he begun laughing. He was like, you are not genuinely gonna like this.”
What started as a very simple computer system mend before long turned into a troubling revelation, an “astounding” and “disgusting” volume of do-it-yourself pornography. In addition, Mac Isaac also uncovered a PDF indicating that Hunter had made $1.2 million for Burisma, a non-public vitality corporation in Ukraine.
After exploring Burisma and the contents of the laptop computer, John recognized it was time to make contact with the authorities. Mac Isaac fulfilled with FBI brokers, but they seemed to be in no rush to search into the notebook or choose action.
“I think that was my initially indicator that perhaps the FBI was extra fascinated in returning the laptop to the former operator and guarding the Bidens than they were being shielding me or getting this to the suitable channel,” he mentioned.
So, Mac Isaac modified his technique. That is when he arrived in get hold of with Bob Costello, Rudy Giuliani’s lawyer. The rest is background. The notebook turned an merchandise of interest across the political spectrum. But, just prior to the 2020 presidential election, Major Tech determined to censor its contents.
Fb stated they were waiting around on point-checkers (who in no way arrived) to confirm the authenticity of the laptop. Meanwhile, Twitter blocked a New York Article write-up backlink breaking down the contents of the laptop computer from remaining shared. The Post’s account was even temporarily banned from the platform.
Regardless of all the controversy bordering the notebook, Hunter doesn’t appear to be to recall how it wound up at that personal computer repair service shop. In his memoir, Hunter only remembers obtaining a simply call from his mother Jill, inquiring him to come residence.
WHO IS HUNTER BIDEN? Decide JEANINE PIRRO DIVES INTO THE Sad BACKSTORY OF THE PRESIDENT’S SON
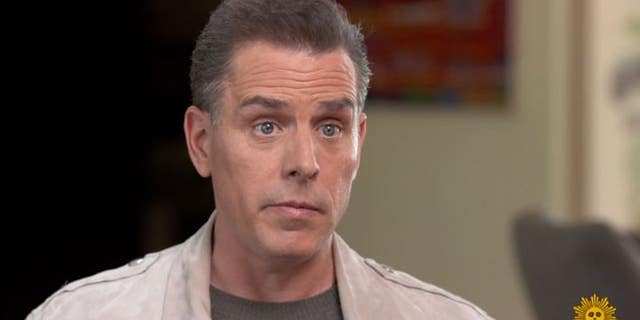
Credit: CBS Sunday Early morning
“I walked into the house, vivid and homey as constantly, and right away noticed my 3 daughters. I understood then that a little something was up,” Hunter recalled.
Hunter then noticed his father and two counselors





