Getty Illustrations or photos
If you have at any time anxious about the privacy of your sensitive info when in search of a laptop or cellular phone repair service, a new research implies you have very good cause. It discovered that privacy violations transpired at least 50 percent of the time, not astonishingly with female customers bearing the brunt.
Scientists at College of Guelph in Ontario, Canada, recovered logs from laptops following acquiring overnight repairs from 12 commercial outlets. The logs showed that specialists from 6 of the areas had accessed personal data and that two of individuals stores also copied info onto a particular machine. Equipment belonging to females were far more most likely to be snooped on, and that snooping tended to seek additional sensitive facts, together with both sexually revealing and non-sexual pics, documents, and fiscal facts.
Blown away
“We were being blown away by the outcomes,” Hassan Khan, one of the scientists, reported in an job interview. Primarily concerning, he claimed, was the copying of details, which took place through repairs for a person from a male client and the other from a feminine. “We considered they would just appear at [the data] at most.”
The amount of snooping might really have been higher than recorded in the examine, which was conducted from October to December 2021. In all, the scientists took the laptops to 16 stores in the larger Ontario region. Logs on units from two of individuals visits weren’t recoverable. Two of the repairs ended up done on the location and in the customer’s existence, so the technician had no chance to surreptitiously look at personal information.
In three circumstances, Home windows Speedy Access or Just lately Accessed Files experienced been deleted in what the researchers suspect was an try by the snooping technician to deal with their tracks. As observed before, two of the visits resulted in the logs the researchers relied on currently being unrecoverable. In a person, the researcher stated they experienced put in antivirus software package and performed a disk cleanup to “remove numerous viruses on the system.” The scientists acquired no rationalization in the other situation.
Here’s a breakdown of the 6 visits that resulted in snooping:
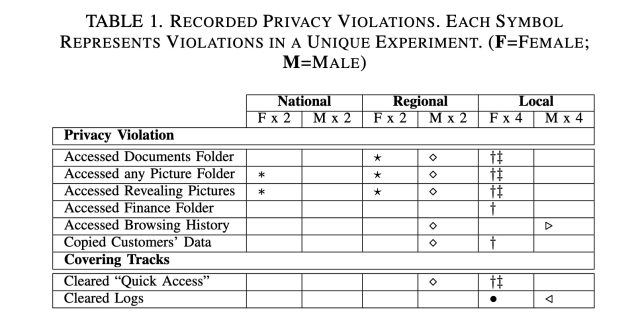
Ceci, Stegman, Khan
The laptops were being freshly imaged Home windows 10 laptops. All had been absolutely free of malware and other flaws and in perfect performing affliction with a single exception: the audio driver was disabled. The researchers selected that glitch for the reason that it demanded only a simple and reasonably priced mend, was effortless to create, and did not require obtain to users’ personalized files.
Half of the laptops were configured to surface as if they belonged to a male and the other 50 % to a female. All of the laptops have been established up with email and gaming accounts and populated with browser record throughout numerous weeks. The scientists additional paperwork, both of those sexually revealing and non-sexual images, and a cryptocurrency wallet with credentials.
The




