At any time get that sensation you are becoming viewed? If you have at the moment got the Screencastify Chrome extension energetic, you could be. A flaw the company claimed was ‘fixed’ may well nevertheless allow malicious actors to entry unsuspecting users’ webcam and desktop activity, and report it for no matter what they see in good shape.
You’ve in all probability witnessed these ‘sextortion’ e-mails: “We have a recording of you executing X, Y, Z. Deliver us $10,000 in some obscure cryptocurrency or we are going to launch the vid for all the earth to see.”
With more than 10,000,000 installs, Screencastify caters to a range of corporations such as Webflow, Teachable, Atlassian, Netlifyrunning, Marketo, and ZenDesk. It is an extension that lets people document, edit and post online video information for do the job and college initiatives, so end users contain lecturers, and schoolchildren at many levels of their schooling. I can only envision the stress from mom and dad when the vulnerability was found out, and their possible fury being aware of it nevertheless has not been effectively set.
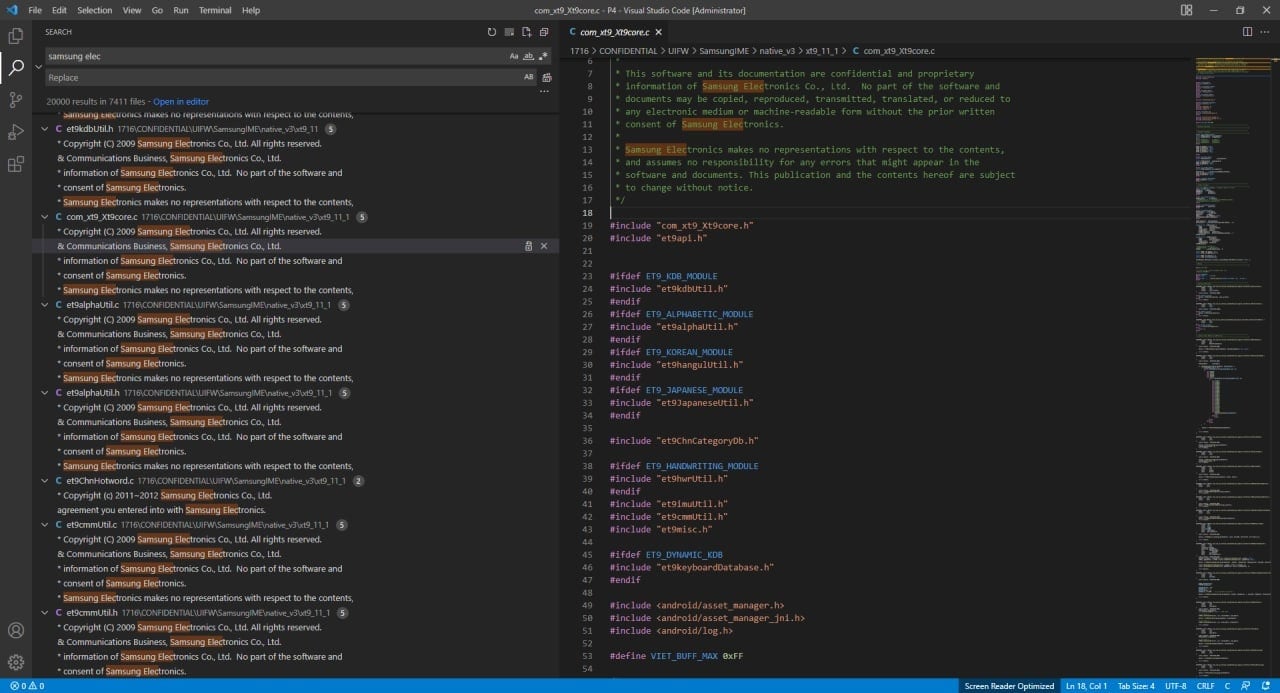
According to Bleeping Computer system (opens in new tab), a cross-internet site scripting (XSS) vulnerability in the Screencastify software was noted by security researcher Wladimir Palant on February 14, 2022. Devs at the rear of the Chrome extension instantly sent out a supposed deal with, but Palant has designed it crystal clear the app is continue to placing customers in a vulnerable posture for exploitation, and extortion.
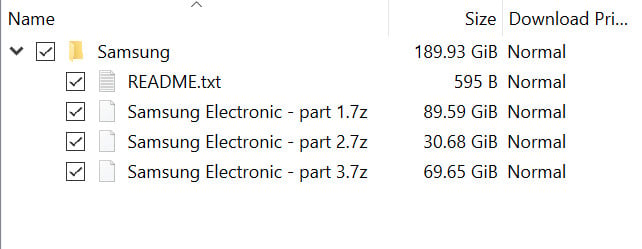
On setting up Screencastify, it asks to access your Google Generate and helps make a long-lasting Google OAuth entry token for the company’s account. The cloud folders produced with the token, in which all the customers video jobs are saved, are allegedly allow unhidden.
Chrome’s desktopCapture API and tabCapture permissions are also granted quickly when you put in the software, which means it has the potential to file your desktop also.
On prime of this, the software’s WebRTC API authorization is only asked for once, this means the capture features are constantly enabled from the get go, unless you switch the placing to ‘ask permission’ just about every time. Even then, Palant uncovered that hackers could not only steal the authentication token, but also use the Screencastify application to report with out notifying the user at all.
“Not significantly appears to have modified listed here, and I could verify that it is nonetheless attainable to commence a webcam recording devoid of any visible clues,” Palant describes in their research blog put up (opens in new tab).
“The issue was found in the mistake website page shown if you currently submitted a video to a problem and were being trying to submit another one.” And given that the mistake page has a fastened handle, “it can be opened directly instead than triggering the error affliction.”
Equally Bleeping Laptop and Palant have contacted Screencastify, but to no avail.
This is a rapid glance in excess of the Screencastify privateness policy:
“We