Personal computer Historical past Museum
It’s not uncommon to listen to that a distinct army engineering has found its way into other applications, which then revolutionized our lives. From the imaging sensors that were being refined to fly on spy satellites to sophisticated aerodynamics applied on each and every modern jetliner, quite a few of these suggestions originally sounded like terrible science fiction.
So did this one.
Take into consideration the subsequent scenario:
To protect the United States and Canada, a large array of interconnected radars would be established up across the two nations. Related by higher-pace backlinks to a dispersed network of desktops and radar scopes, Air Pressure staff scan the skies for unexpected activity. 1 day, an unknown aircraft is learned, traveling more than the Arctic and heading towards the United States. A brief check of all regarded commercial flights principles out a planeload of holiday tourists lost in excess of the Northern Canadian tundra. At headquarters, the flight is selected as a bogey, as all makes an attempt to contact it have unsuccessful. A regimen and usually uneventful intercept will hence fly alongside to identify the plane and report registration info.
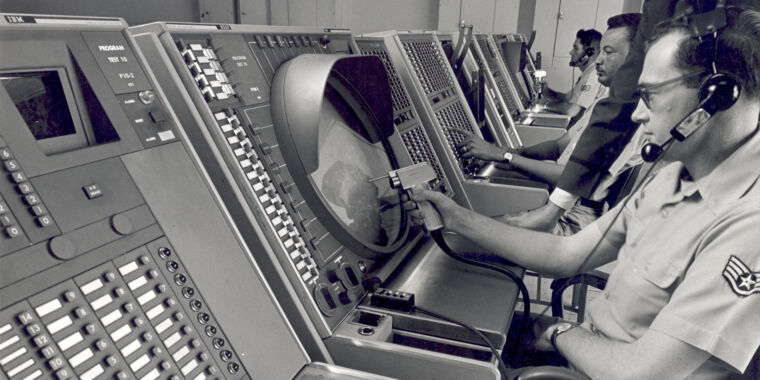
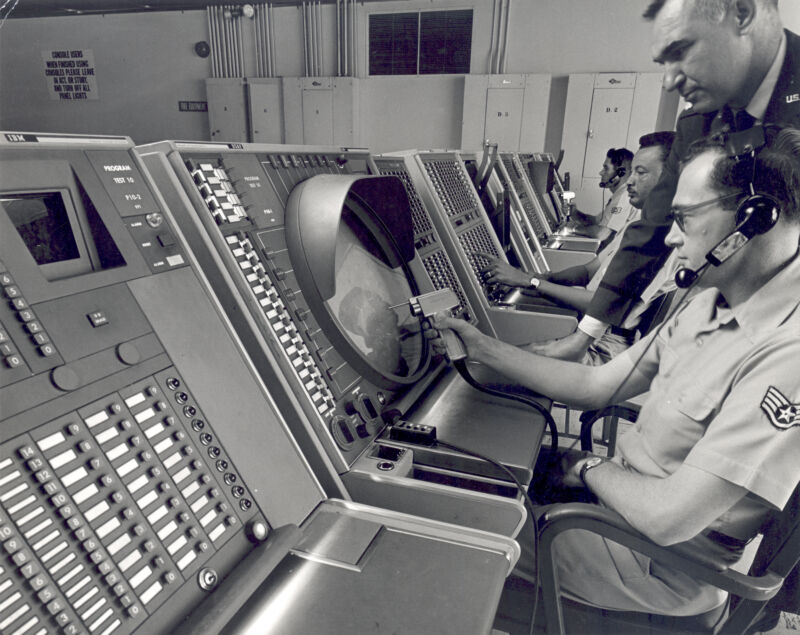
Ahead of the intercept can be completed, far more aircraft show up around the Arctic an attack is originating from Russia. Readiness is elevated to DEFCON 2, a single move down below that of nuclear war. Controllers across the state commence to get a high-stage photo of the assault, which is projected on a big screen for senior army leaders. At a console, the intercept director clicks a few icons on his display screen, assigning a fighter to its focus on. All the critical information and facts is radioed instantly to the aircraft’s laptop or computer, without chatting to the pilot.
By the time the pilot is buckled into his seat and taxiing to the runway, all the knowledge needed to damage the intruder is loaded onboard. A callout of “Dolly Sweet” from the pilot acknowledges that the knowledge load is very good. Lifting off the runway and raising the gear, a flip of a change in the cockpit turns the flight over to the personal computers on the ground and the radar controllers watching the bogey. A massive display screen in the cockpit supplies a map of the space and materials important situational awareness of the concentrate on.
The total intercept is flown fingers-off, with the pilot only modifying the throttle. The plane, updated with the hottest information from floor controllers, adjusts its system to intercept the enemy bomber. Only when the target is inside the fighter’s radar assortment does the pilot think control—then selects a weapon and fires. Soon after a swift evasive maneuver, manage returns to the autopilot, which flies the fighter back again to foundation.
This isn’t an excerpt from a dystopian graphic novel or a cut-and-paste from a current aerospace magazine. In truth, it’s all historic background. The technique described previously mentioned was identified as SAGE—and it was executed in 1958.
SAGE, the Semi-Automatic Ground Natural environment, was the answer to the challenge of defending North America from Soviet bombers through the Cold War. Air protection was mainly ignored soon after Globe War II, as write-up-war demilitarization gave way to the explosion of the buyer financial state. The exam of the initial Soviet atomic bomb improved that perception of complacency, and the US felt a new urgency to carry out a centralized defense technique. The expected assault situation was waves of fast-relocating bombers, but in the early 1950’s, air defense was regionally fragmented and lacked a central coordinating authority. Countless experiments tried using to occur up with a answer, but the technology of the time simply just wasn’t in a position to meet expectations.
Whirlwind I
In the waning times of World War II, MIT researchers tried to layout a facility for the Navy that would simulate an arbitrary aircraft layout in order to examine its dealing with properties. Initially conceived as an analog computer, the solution was abandoned when it grew to become obvious that the gadget would not be fast or correct more than enough for this sort of a range of simulations.
Interest then turned to Whirlwind I, a innovative electronic technique at MIT, with a 32-little bit word duration, 16 “math units,” and 2,048 terms of memory built from mercury hold off traces. Importantly, Whirlwind I experienced a complex I/O method it launched the notion of cycle thieving in the course of I/O functions, where the CPU is halted through facts transfer.
Following a several many years, the Navy lost desire in the undertaking because of to its substantial expense, but the Air Force evaluated the program for air protection. Soon after modifying quite a few radars in the Northeast United States to send digital coordinates of targets they ended up tracking, Whirlwind I proved that coordinating intercepts of bombers was realistic. Crucial to this practicality ended up substantial-trustworthiness vacuum tubes and the development of the to start with main memory. These two developments lessened the machine’s in any other case sizeable downtime and greater processing before long created Whirlwind I 4 occasions faster than the primary structure.